Anomaly Detection in Financial Transactions by AI ML
A company wants to ensure the integrity of its financial transactions and quickly identify any unusual or suspicious activities that may indicate fraud or errors.
Solution
Implement a machine learning-based anomaly detection system that learns the normal patterns of financial transactions and flags any deviations from these patterns.
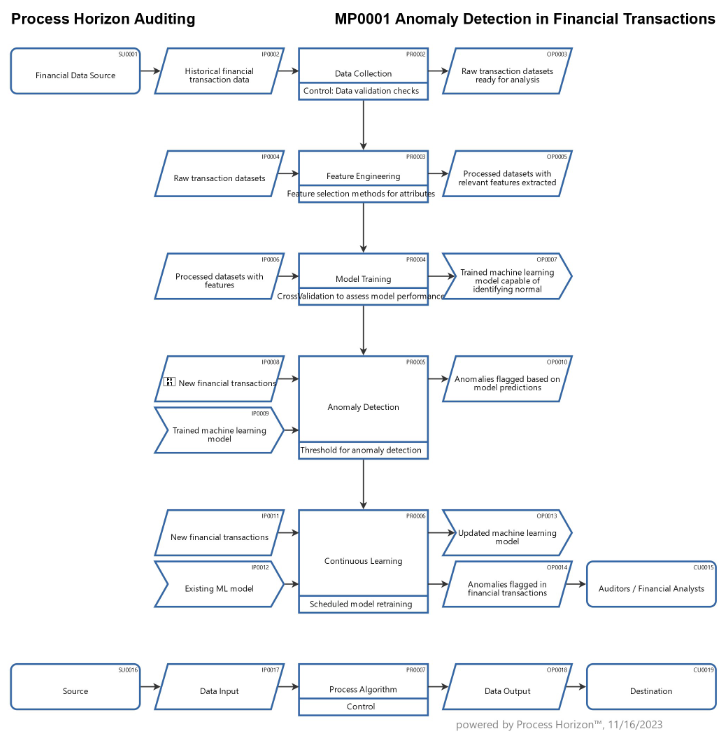
Process steps
- Data Collection: Gather historical data on financial transactions, including details such as transaction amount, time, location, and any other relevant features.
- Feature Engineering: Identify and extract relevant features from the transaction data, such as transaction frequency, average transaction amount, and time of day.
- Model Training: Train a machine learning model, such as an unsupervised learning algorithm on the historical data to learn the normal patterns of transactions. The model will identify patterns and relationships within the data without explicit fraud labels.
- Anomaly Detection: Apply the trained model to new transactions. The algorithm will assign a score or probability to each transaction, indicating how well it fits the learned normal patterns. Transactions with scores exceeding a predefined threshold are flagged as anomalies.
- Continuous Learning: Periodically update the model with new data to adapt to changes in transaction patterns over time. This ensures the model remains effective in identifying anomalies as the system evolves.
Benefits
- Efficiency: The AI algorithm can process large volumes of transactions quickly, automating the initial screening process and allowing auditors to focus on investigating flagged transactions.
- Early Detection: Anomaly detection algorithms can identify irregularities in real-time, enabling prompt action to address potential issues before they escalate.
- Adaptability: The model can adapt to changing transaction patterns, making it robust against new fraud techniques or variations in legitimate transaction behavior.
By incorporating such AI algorithms into the auditing process, organizations can enhance the accuracy and efficiency of their financial audits while reducing the risk of undetected anomalies or fraudulent activities.
Using the following link you can access this sandbox process model in the ProcessHorizon web app and adapt it to your needs (easy customizing) and export or print the automatically created visual process map as a PDF document or share it with your peers: https://app.processhorizon.com/enterprises/rufaav5NrDapAxnu19esZ388/frontend

